Cybersecurity
Improving your cyber resilience
Today, many organizations are digital and data-driven. This makes cybersecurity more important than ever, but also more difficult than ever. How can you quickly detect threats? How should you respond efficiently, and which measures should be in place to effectively mitigate risks?
Building a cyber resilient business requires a multifocal approach taking into account people, processes and technology.
Organizations face increasingly complex challenges when it comes to cybersecurity
Ubiquity
Everything is digital, everything is hyperconnected and cyber is introduced in all layers of the organization. Thus, ingredients for cyber attacks are everywhere.Compliance needs
Strong compliance requirements are no longer limited to healthcare and finance. Every company needs security adapted to strict regulations.Digital ecosystems
Data access is becoming more complex and extended into different parts of your organization. Data-exchange activities rev up the need for solid security and data protection solutions.Growing risk of attack
Organized criminal networks are well-financed and increasingly professional. Your security measures need to be up to par against the proliferation of cyber attacks.Cybersecurity requires a full-scale approach
Being cyber resilient is not a matter of just buying or implementing one solution. Threats continuously evolve, and so should your cyber security strategy.
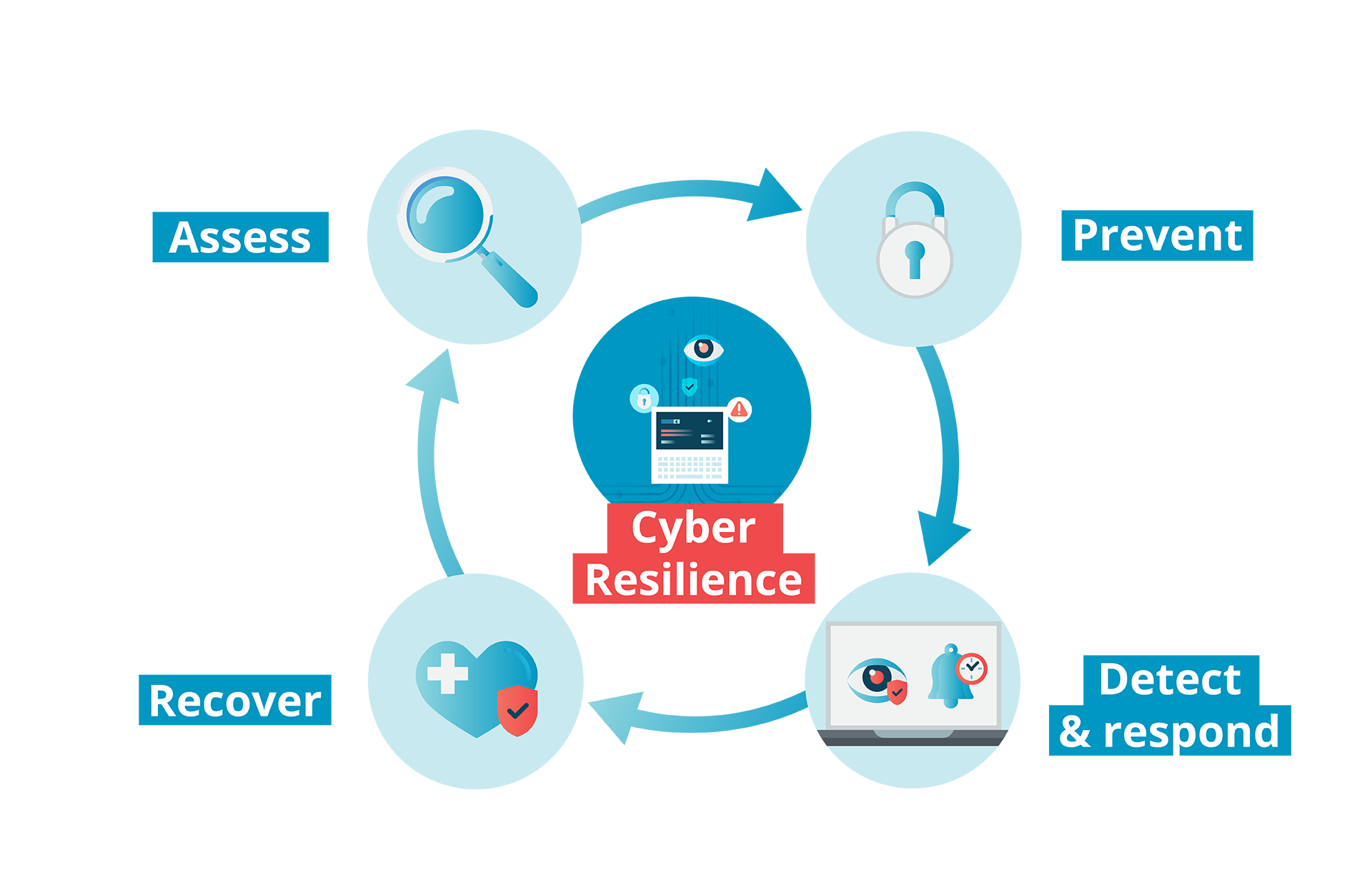
By introducing a continuous process of security improvement and adaption, it is possible to constantly assess the situation and act accordingly to protect your business and stay in control.
We manage security solutions for you, from implementation to 24x7 management and monitoring to ensure your security infrastructure stays up-to-date without increasing your workload.
Our approach to cybersecurity assures focus on what matters most to your business: comprehensive preventive measures, 360° monitoring, detection, and response as well as fast recovery in case your business is compromised.
Assess
Robust security starts with a clear and accurate assessment of your current security landscape and potential risks. This is a continuous process of reevaluation that will help you prioritize and intelligently apply your security investments and resources.
- Vulnerability & Compliance Management
Vulnerability Management reveals potential vulnerabilities and weaknesses across the assets in your infrastructure and manages the process of prioritizing, remediation and mitigating. Compliance Management helps you reach and maintain conformance to protective controls on your assets.
- Phishing simulation
Simulating potential phishing threats – such as simulated phishing emails attempting to retrieve passwords or sending dubious links to see if they get clicked on – will help to gain insight in your phishing attack surface. This is a structured long-term approach. The results of these automatic simulations inform your next actions.
- Penetration testing
As part of the assessment, penetration tests attempt to breach your security to expose possible entries via channels such as your Internet presence through web applications, internal network, server, red teaming or employees.
- Privilege Account Discovery
Protecting your privilege accounts is key. This assessment helps you to detect privileged accounts on your assets.
- Cyber Security Assessment
Understanding your attack surface and where to prioritize your security investments is a key starting point. The Cyber Security Assessment examines the maturity of your organization and helps defining an effective cyber security roadmap.
Prevent
Prevention is all about taking the right measures to protect your assets from – and reduce the impact of - breaches and security issues on every touchpoint and connection with focus on people, processes and technology.
- Network, infrastructure & cloud security
Technical security measures to protect your network, infrastructure, and cloud. These solutions include a broad an integrated spectrum of technologies including next-generation firewalls, detection tools, network access control, mail security, DDOS protection and many others.
- Privileged access management (PAM)
Employees who have privileged access to business systems (system controllers, management…) pose greater security risks. PAM identifies and controls such elevated access across the enterprise and significantly reduces the organization's attack surface. Delivered as-a-service allows companies to consume the PAM service in a cost-effective way.
- Advanced email security (DMARC)
Delivered as-a-service DMARC provides an advanced layer for your email security.
Detect and respond
Every second counts after a security issue has been detected. That’s why detection and response go hand in hand. Our approach combines intelligent tools and leading threat intelligence with human analysis to provide a round-the-clock Managed Detection & Response capability.
- Managed detection & response (MDR)
Managed Detection & Response is a 24x7 service combining intelligent tools and technologies with leading threat intelligence, proven processes and human security expertise. Private or public cloud infrastructures, workplace or server environments, IT or OT environments are all monitored continuously, for robust and reliable security detection that assures immediate response to possible threats.
- 24/7 security operating center (SOC) guarantees full awareness of everything that’s going on in your environment. Our experts monitor your environment, proactively anticipate possible threats 24/7 and ensure a fast and effective security incident response.
- Managed Security Analytics analyses information from a disparate set of sources (Network, Infrastructure, Applications, Users, …) to make intelligent security incident detections. It automatically recognizes suspicious activities and leverages leading Threat Intelligence allowing our SOC analysts to respond fast.
- Endpoint Detection & Response adds advanced threat detection and immediate response on endpoints including both servers and digital workplaces.
- Network Detection & Response completes Managed Security Analytics and EDR with a Detection & Response service to allow monitoring networks for suspicious behavior and respond to detection of malicious actors in the network.
Delivered as-a-service our modular approach allows to focus on your most critical environments, scale up/down when needed and ensure a cost-effective solution to help you protecting your business.
- Managed Endpoint detection & response (EDR)
As a standalone and cost-effective service our Endpoint detection & response service detects threats on a broad spectrum of endpoints. Detection & Response takes place close to where the danger is and ensures a fast and effective response restricting adversary access and further damage.
Recover
When it comes to cybersecurity, always consider the worst-case scenario: assume something will go wrong at some point in time. When it does, you need a plan to limit damage and get your business back up and running as quickly as possible, and with minimal or no data loss.
- Backup & restore
When your data is safely stored on an external platform, it is possible to quickly restore your data and operations in case of a breach. This service contains a runbook enabling you to rapidly and accurately estimate and limit damage to your IT assets.
A recovery readiness assessment helps to get a view on your capabilities to recover fast and effectively.
Reduce cybersecurity risks
This e-book provides you with a step-by-step guide to reducing cyber security risks in a cost-effective manner; including detect and response best practices.
Security advisory and response
We offer expertise and consultancy for your company at every milestone along the road to cyber resilience – from personnel requirements to policy and beyond. Our security advisory and response services guarantee a personalized and adapted approach to cybersecurity that enables you to continuously improve your security measures.
Our Security Advisors can also complement our managed services to provide an even more close cooperation.
Insights and resources
Why choose Cegeka?
Security in close cooperation
Our approach combines the scale of a managed security provider with the proximity of security expertise ensuring our capability is adapted to your context and incident response is most effective. A phased and modular approach allows to adapt our solutions to different requirements and budgets.
We are a one-stop-shop in security
From assessment to detection and response, our unique combination of 24/7 human and automated analytics ensures a full-scale approach to your cybersecurity.
A proven track record
We apply use cases from all clients to continuously build and improve our security intelligence. That means you profit from the expertise gathered through all our clients.
We are technology agnostic
We’re not tied down to one or a few tech partners. We select and apply leading technologies and innovative tools, you can count on A-grade security.





Fabrice Wynants
Director Security & IAM Solutions